Push Sender node
Sends push notification messages to a device for multi-factor authentication.
Configure the AM Push Notification Service for the realm before using this node.
For information on provisioning the credentials used by the service, refer to How To Configure Service Credentials (Push Auth, Docker) in Backstage in the Knowledge Base.
To determine whether the user has a registered device, the flow must have included the username in the shared state, for example, by using a Platform Username node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Authenticators
The push-related nodes integrate with the ForgeRock Authenticator app for Android and iOS.
Third-party authenticator apps are not compatible with ForgeRock’s push notification functionality.
Outcomes
-
Sent -
Not Registered -
Skipped -
Failure
Evaluation continues along the Sent outcome path
if the push notification was successfully sent to the handling service.
If the user doesn’t have a registered device, evaluation continues along the Not Registered outcome path.
If the user chooses to skip push authentication, evaluation continues along the Skipped outcome path.
The node displays the Failure outcome only if you enable the Capture failure configuration option. In this
case, evaluation proceeds along the Failure path if there’s an error during execution of the node.
Properties
| Property | Usage |
|---|---|
Message Timeout |
Specifies the number of milliseconds the push notification message will remain valid. The Push Result Verifier node rejects responses to push messages that have timed out. |
User Message |
Specifies the optional message to send to the user. You can provide the message in multiple languages by specifying the locale in the The locale selected for display is based on the user’s locale settings in their browser. Messages provided in the node override the defaults provided by AM. The following variables can be used in the
Example: |
Remove 'skip' option |
Enable this option in the node to make the push authentication mandatory. When disabled, the user can skip the push authentication requested by the node,
and evaluation continues along the Default: Disabled |
Share Context info |
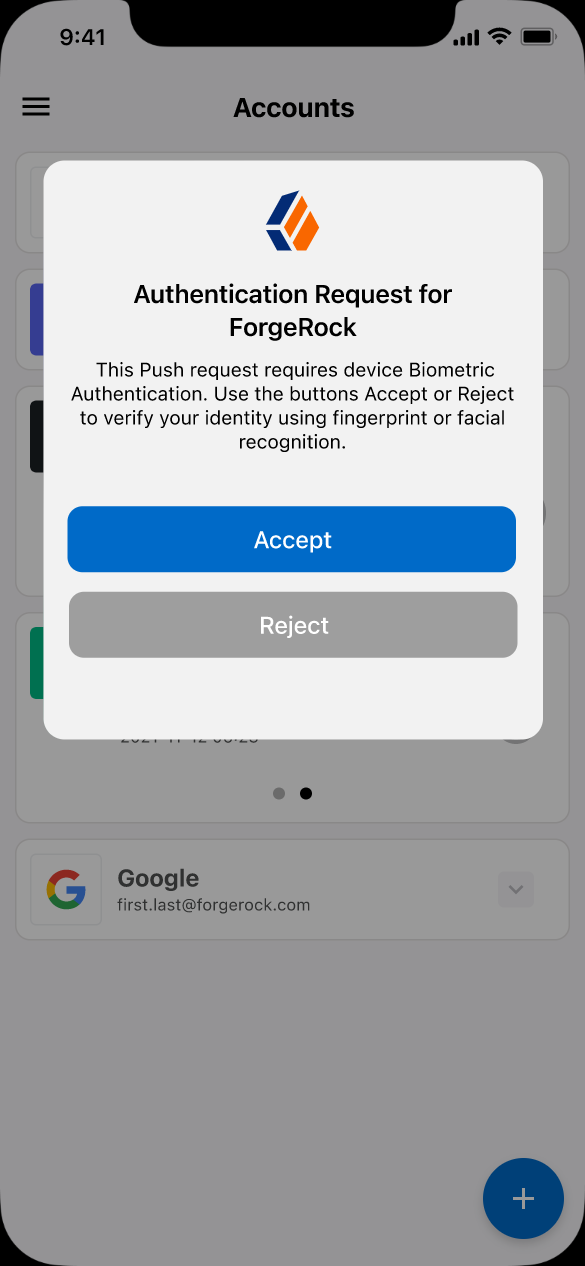
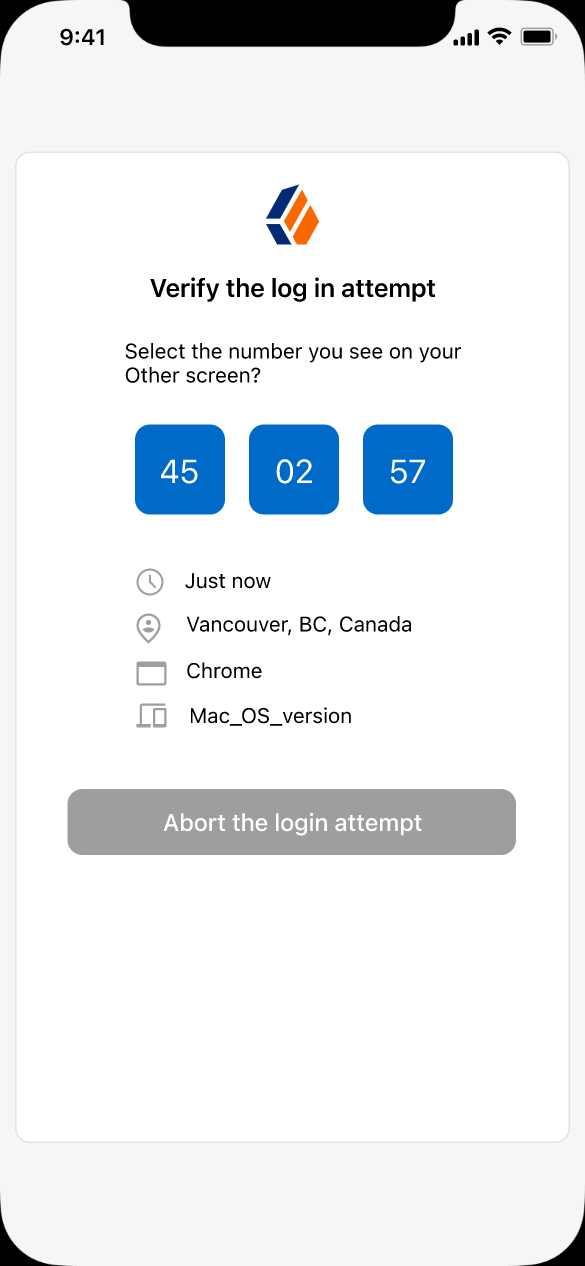
If enabled, context data such as For example: The ForgeRock Authenticator displays this additional information to the user to help verify that the request is genuine and initiated by them. 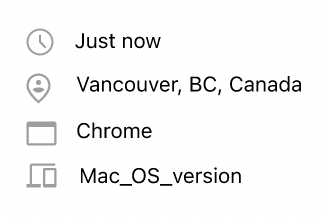
Figure 1. Context information in the ForgeRock Authenticator
For the location attribute to be set, the flow must contain a Device Profile Collector node with Collect Device Location enabled. |
Custom Payload Attributes |
Specify shared state objects to be included in the message payload sent to the client.
The size of the payload must not exceed 3 Kb or a To add a custom attribute, enter the shared state object name in the text field and click Add. Repeat for each object you want to include in the payload. |
Push Type |
Select the type of the push authentication the user must perform on their device to continue the journey. Possible values are:
The actions the user performs vary depending on the selected option. Refer to Respond to push notifications. |
Capture failure (optional) |
If enabled, and the node fails to send the Push Notification, the journey skips the node. The journey stores the reason
for the failure in the Possible failure reasons include |
Example
The following example shows one possible implementation of multi-factor push authentication:
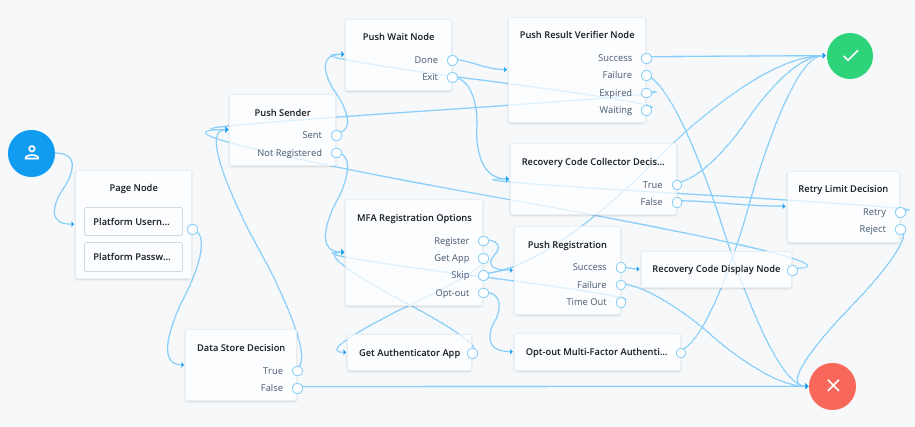
Node connections
| Source node | Outcome path | Target node |
|---|---|---|
Page Node containing: Platform Username, Platform Password |
→ |
Data Store Decision |
Data Store Decision |
True |
Push Sender |
False |
Failure |
|
Push Sender |
Sent |
Push Wait |
Not Registered |
MFA Registration Options |
|
Push Wait |
Done |
Push Result Verifier |
Exit |
Recovery Code Collector Decision |
|
Push Result Verifier |
Success |
Success |
Failure |
Failure |
|
Expired |
Push Sender |
|
Waiting |
Push Wait |
|
MFA Registration Options |
Register |
Push Registration |
Get App |
Get Authenticator App |
|
Skip |
Success |
|
Opt-out |
Opt-out Multi-Factor Authentication |
|
Recovery Code Collector Decision |
True |
Success |
False |
Retry Limit Decision |
|
Push Registration |
Success |
Recovery Code Display Node |
Failure |
Failure |
|
Time Out |
MFA Registration Options |
|
Get Authenticator App |
→ |
MFA Registration Options |
Opt-out Multi-Factor Authentication |
→ |
Success |
Retry Limit Decision |
Retry |
Recovery Code Collector Decision |
Reject |
Failure |
|
Recovery Code Display Node |
→ |
Push Sender |
After verifying the user’s credentials, evaluation continues to the Push Sender node.
If the user has a registered device:
-
AM sends a push to their registered device.
-
The Push Wait node pauses authentication for 5 seconds, during which time the user can respond to the push notification on their device; for example, by using the ForgeRock Authenticator application.
-
If the user responds positively, they are authenticated successfully and logged in.
-
If the user responds negatively, they are not authenticated successfully and do not receive a session.
-
If the push notification expires, AM sends a new push notification.
Use a Retry Limit Decision node to constrain the number of times a new code is sent. -
If the user has not yet responded, the flow loops back a step and the Push Wait node pauses authentication for another 5 seconds.
If the user exits the Push Wait node, they can enter a recovery code in order to authenticate.
For this situation, configure the Exit Message property in the Push Wait node with a message, such as
Lost phone? Use a recovery code. -
A Retry Limit Decision node allows three attempts at entering a recovery code before failing the authentication.
If the user does not have a registered device:
-
The MFA Registration Options node presents the user with the following options:
- Register Device
-
The flow continues to the Push Registration node, which displays the QR code that should be scanned with a suitable authenticator application.
- Get the App
-
The flow continues to the Get Authenticator App node, which displays the links needed to obtain a suitable application, such as the ForgeRock Authenticator.
- Skip this step
-
Displayed only if the node configuration lets the user skip. In this example, skipping is linked to the
Successoutcome. Alternatively, an Inner Tree Evaluator node could have been used for authentication. - Opt-out
-
Displayed only if the node configuration allows the user to skip or opt out. Evaluation continues to the Opt-out Multi-Factor Authentication node, which updates the user’s profile to skip MFA with push in the future. In this example, after updating the profile the flow continues to the Success node.
-
The user registers the device with the Push Registration node.
After registration, the recovery codes are displayed to the user for safekeeping, and evaluation continues with the Push Sender node to start push notification.
|
To manage push devices, the user must log in using either the device or a recovery code. Learn more in Manage devices for MFA. |
Respond to push notifications
The default Push Type setting is Tap to Accept. This requires the user to tap to either Accept or Reject in the ForgeRock Authenticator.
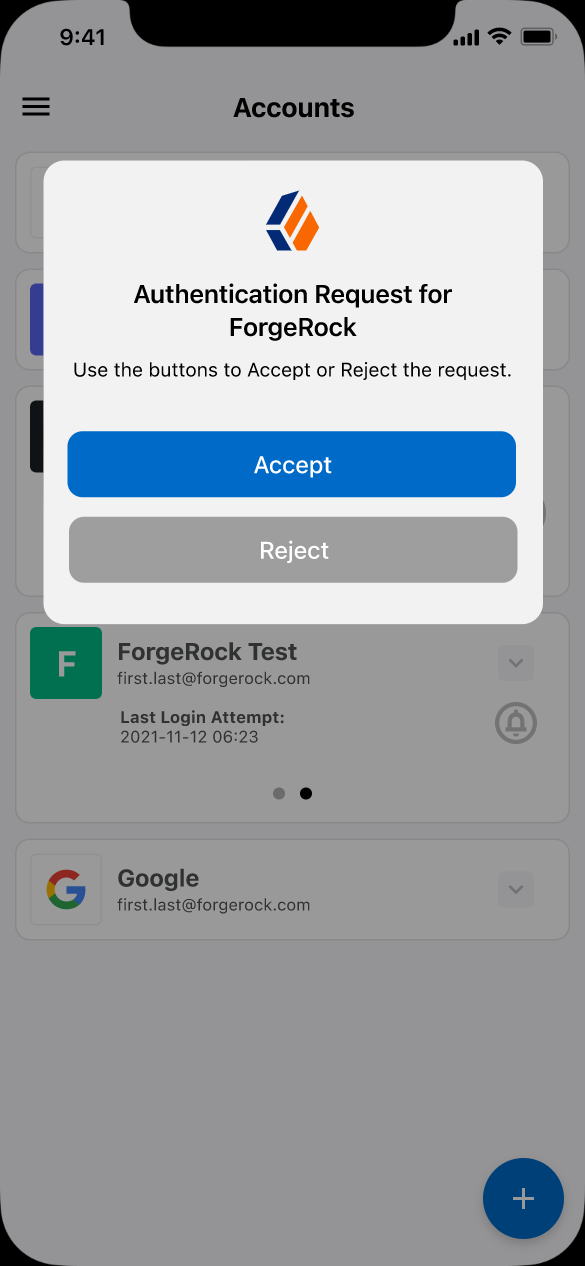
Research shows that users might accept a push authentication without fully checking if it is legitimate. To reduce the chances of a user accepting a malicious push authentication attempt, you can configure two additional push types:
Display Challenge Code-
Requires the user to select one of three numbers displayed on their device. This selected number must match the code displayed in the browser for the request to be verified.
Use Biometrics to Accept-
Requires the user’s biometric authentication to process the notification, after tapping
AcceptorReject.