Configuring SSL for client-side connection or external APIs
ASE supports both TLS 1.2 and SSLv3 for external APIs.
Before you begin
By default, SSLv3 is disabled due to security vulnerabilities. To change the default and enable SSLv3, stop ASE and then change enable_sslv3 to true in ase.conf file. Restart ASE to activate SSLv3 protocol support. SSLv3 is only supported for client to ASE connections, not ASE to backend server connections.
; SSLv3 enable_sslv3=true
About this task
OpenSSL is bundled with ASE. The following are the version details:
-
RHEL: OpenSSL 1.0.2k-fips 26 Jan 2017
-
Ubuntu: OpenSSL 1.0.2g 1 Mar 2016
You can configure SSL in ASE for client-side connection using one of the following methods:
-
Using a CA-signed certificate
-
Using a self-signed certificate
-
Importing an existing certificate
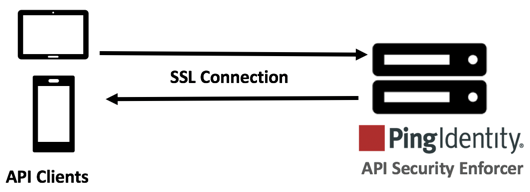
The steps provided in this section are for the certificate and key generated for connections between the client and ASE as depicted in the diagram below:
In a cluster setup:
-
Stop all the ASE cluster nodes
-
Configure the certificate on the management node.
For more information on management node, see API Security Enforcer Admin Guide.
-
Start the cluster nodes one by one for the certificates to synchronize across the nodes
|
You can also configure for Management APIs. For more information on configuring SSL for management APIs, see Configure SSL for Management APIs. |
Using a CA-signed certificate
About this task
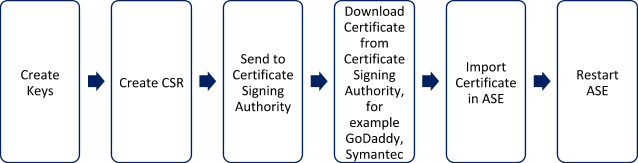
To use a Certificate Authority (CA)-signed SSL certificates, follow the process shown below to create a private key, generate a certificate signing request (CSR), and request a certificate:
|
ASE internally validates the authenticity of the imported certificate. |
Steps
-
Create a private key.
/optCDO:/content/authoring/nrc1651605112856.image/pingidentity/ase/bin/cli.sh create_key_pair -u admin -p Warning: create_key_pair will delete any existing key_pair, CSR and self-signed certificate Do you want to proceed [y/n]:y OK, creating new key pair. Creating DH parameter may take around 20 minutes. Please wait Key created in keystore dh param file created at /opt/pingidentity/ase/config/certs/dataplane/dh1024.pem
ASE command-line interface (CLI) is used to create a 2048-bit private key and to store it in the key store.
-
Create a CSR.
/opt/pingidentity/ase/bin/cli.sh create_csr -u admin -p Warning: create_csr will delete any existing CSR and self-signed certificate Do you want to proceed [y/n]:y please provide following info Country Code >US State > Colorado Location >Denver Organization >Pingidentity Organization Unit >Pingintelligence Common Name >ase Generating CSR. Please wait... OK, csr created at /opt/pingidentity/ase/config/certs/dataplane/ase.csr
Result:
ASE takes you through a CLI-based interactive session to create a CSR.
-
Upload the CSR created in step 2 to the CA-signing authority’s website to get a CA-signed certificate.
-
Download the CA-signed certificate from the CA-signing authority’s website.
-
Use the CLI to import the signed CA certificate into ASE. The certificate is imported into the key store.
/opt/pingidentity/ase/bin/cli.sh import_cert <CA signed certificate path> -u admin -p Warning: import_cert will overwrite any existing signed certificate Do you want to proceed [y/n]:y Exporting certificate to API Security Enforcer... OK, signed certificate added to keystore
-
Restart ASE by first stopping and then starting ASE.
Using ABS self-signed certificates with Postman
API Behavioral Security (ABS) ships with a self-signed certificate.
About this task
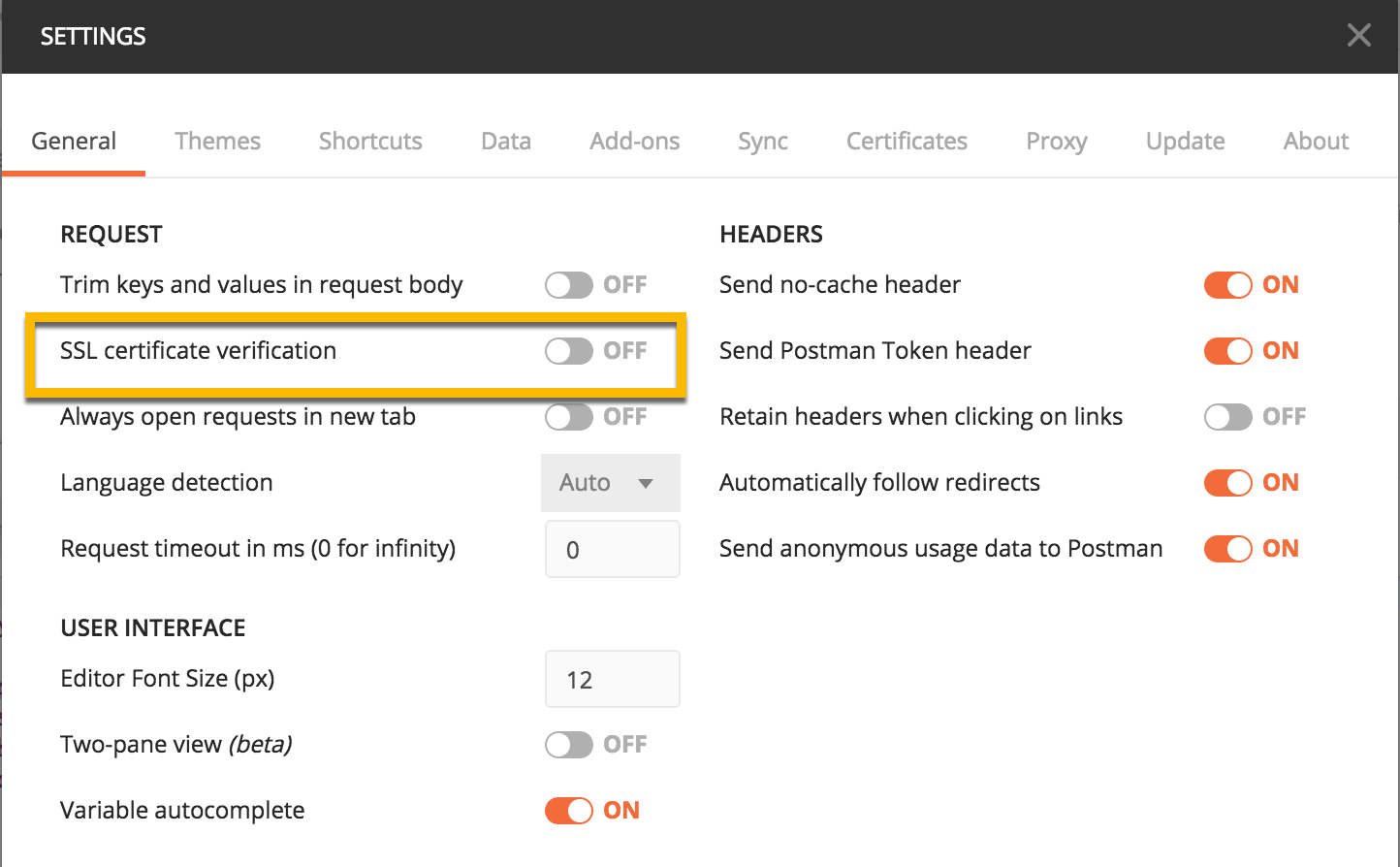
If you want to use Postman with the self-signed certificate of ABS, you can disable the certificate verification option from Postman’s settings.
Steps
-
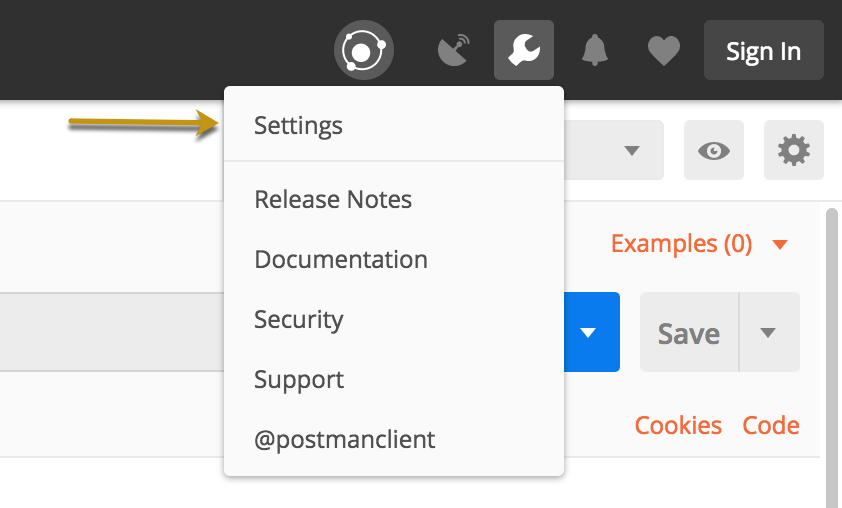
Click on the Wrench icon on the top-right corner of Postman client. A drop-down window is displayed.
-
Select Settings from the drop-down menu:
-
In the Settings window, click the toggle to turn off certificate verification by clicking on the SSL certificate verification button:
Importing an existing certificate and key pair
About this task
The following diagram shows an overview of the steps for importing an existing certificate and key pair.
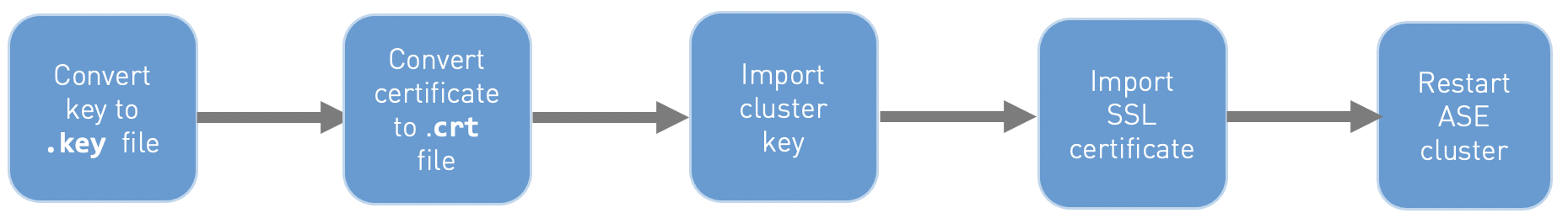
To import an existing certificate and key pair:
Steps
-
Convert the key to a
.keyfile:openssl rsa -in private.pem -out private.key
-
Convert the SSL certificate to a
.crtfile:openssl x509 -in server-cert.pem -out server-cert.crt
-
Import the cluster key into the key store using the following CLI command.
import_key_pair {key_path} [--yes | -y] import key pair for cluster server --yes | -y : import key pair without confirmation prompt -
Import the certificate into the key store using following CLI command:
import_cert {cert_path} [--yes | -y] import CA signed certificate for cluster server --yes | -y : import CA signed certificate without confirmation prompt -
Restart the API Security Enforcer (ASE) cluster for synchronizing the key and the certificate.
For more information on restarting the ASE cluster, see Restart ASE cluster.