Capture client identifiers in inline mode
API Security Enforcer (ASE) identifies attackers for HTTP(s) and WS(s) protocols using five client identifiers:
-
OAuth2 token
-
Cookie
-
IP address
-
API keys
-
Username
|
Username is not configured in the api_metadata object of application programming interface (API) JavaScript Object Notation (JSON). However, ASE supports the extraction of usernames coming in a JSON Web Token (JWT) or custom headers. For more information, see Extract user information from JWT in inline mode and Extract username from custom header in inline mode. For usernames that are not part of either JWTs or custom headers, API Behavioral Security (ABS) AI Engine identifies them based on metadata logged in ASE’s access logs. |
The following sections describe how to configure ASE to capture OAuth2 Tokens and API keys.
Configure ASE support for OAuth2 tokens
ASE supports capturing and blocking of OAuth2 tokens. To enable OAuth2 token capture, set the value of oauth2_access_token to true in the API JSON file. Here is a snippet of an API JSON file with OAuth2 Token capture activated. To disable, change the value to false.
"api_metadata": {
"protocol": "http",
"url": "/",
"hostname": "*",
"cookie": "",
"cookie_idle_timeout": "200m",
"logout_api_enabled": false,
"cookie_persistence_enabled": true,
"oauth2_access_token": true,
"is_token_mandatory": false,
"apikey_qs": "",
"apikey_header": "",
"login_url": "",
"enable_blocking": true,
"api_mapping": {
"internal_url": ""
},
When enable_blocking is true, ASE checks the token against the list of tokens in the allow list and deny list. If the token is in the deny list, the client using the token is immediately blocked. Further, when is_token_mandatory is set totrue, and the incoming request has a missing token, ASE adds the IP address of the client to deny list and blocks the request.
|
For ASE to check and block the client, |
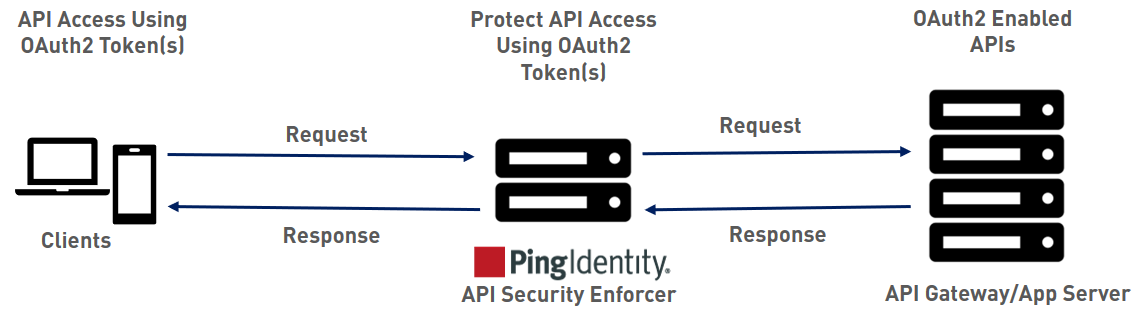
When pattern enforcement violations are detected on an API configured to support tokens, the attacking client token is added to the deny list in real-time, recorded in the ASE access log, and sent to ABS for further analytics. The following diagram shows the traffic flow in an OAuth2 environment:
Configure ASE support for API keys
ASE supports capturing and blocking of API keys. Depending on the API setup, the API key can be captured from the query string or API header. Each API JSON file can be configured with either the query string (apikey_qs) or API header (apikey_header) parameter.
Here is a snippet of an API JSON file showing API Key being configured to capture the API Key from the Query String (apikey_qs).
"api_metadata": {
"protocol": "http",
"url": "/",
"hostname": "*",
"cookie": "",
"cookie_idle_timeout": "200m",
"logout_api_enabled": false,
"cookie_persistence_enabled": true,
"oauth2_access_token": true,
"is_token_mandatory": false,
"apikey_qs": "key_1.4",
"apikey_header": "",
"login_url": "",
"enable_blocking": true,
"api_mapping": {
"internal_url": ""
},
When an API Key is included in the API JSON file, ASE supports blocking of API keys which are manually added to the deny list.